Single Sign-On
Limited control of authentication processes can leave organizations open to security risks.
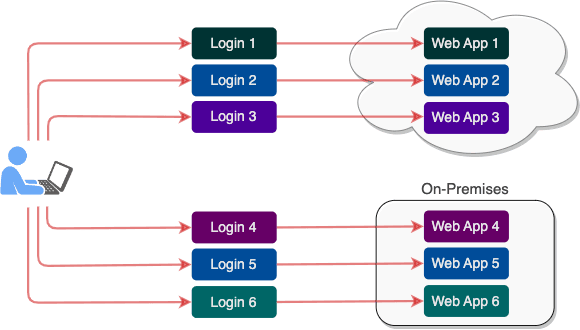
When users access numerous cloud and on-premises applications, they need to enter a separate set of credentials for every application or group of applications. Some groups are integrated through Active Directory, or Google, or another identity provider, and some require individual credentials.
With so many credentials to remember, it’s easy for users to lapse into bad habits, such as making a note of passwords or reusing the same password for many applications.
Both are common approaches. Both introduce security risks.
Solution: ViewDS Cobalt IAM
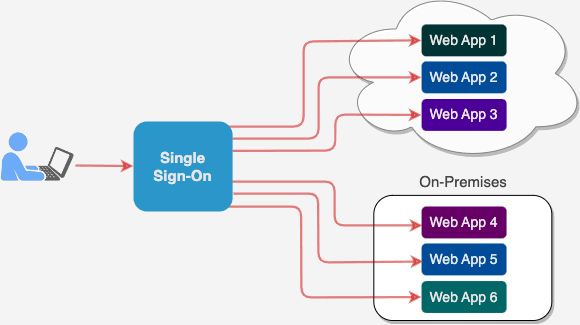
Cobalt is a platform for identity and access management (IAM) that allows you to deliver single sign-on to all your on-premises and cloud applications.
Cobalt IAM can act as the identity provider and single credential store, or leverage the authentication services provided by Okta, Azure Active Directory, or your on-premises Active Directory. Industry-standard protocols, including SAML and OpenID Connect, allow easy integration with your applications.
Cobalt IAM offers seamless access for users, greater control for you, and stronger security for your entire organization.