Authorization Services
For an organization that stores sensitive information, it’s essential to ensure that the right people can access the right data at the right time.
However, managing authorization policy across all your cloud and on-premises applications can be a major challenge.
The legacy approach is to embed entitlement within every application. When a user attempts to access an application, the application interrogates a local copy of the authorization policy to determine the user’s access rights.
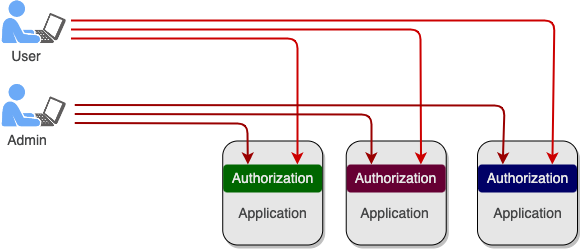
Embedding Authorization is Inefficient, Error-Prone, and Costly
Solution: ViewDS Access Sentinel
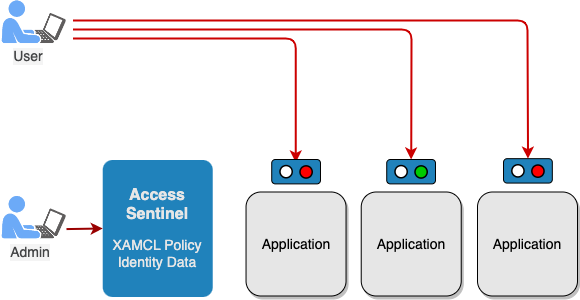
Access Sentinel is a highly efficient authorization server that centralizes the management and processing of authorization policy.
As well as providing a more efficient approach to maintaining and auditing policy, Access Sentinel allows access controls to be applied globally and consistently. Life becomes easier for support staff as they can define policy for all applications in one hit through a single, intuitive user interface.
The world also becomes a little brighter for software developers as they no longer need to write an entitlement layer for each new application. Instead, Access Sentinel provides a lightweight Policy Enforcement Point (PEP) at the application to enforce the access-control decisions made centrally.
Full IAM Solution?
All the features and benefits of Access Sentinel are also provided by ViewDS Cobalt IAM, a comprehensive IAM solution for Cloud Service Providers.



